Getting Started with WebGoat
A quick-start guide to installing WebGoat, a deliberately insecure web application designed to teach web application security.

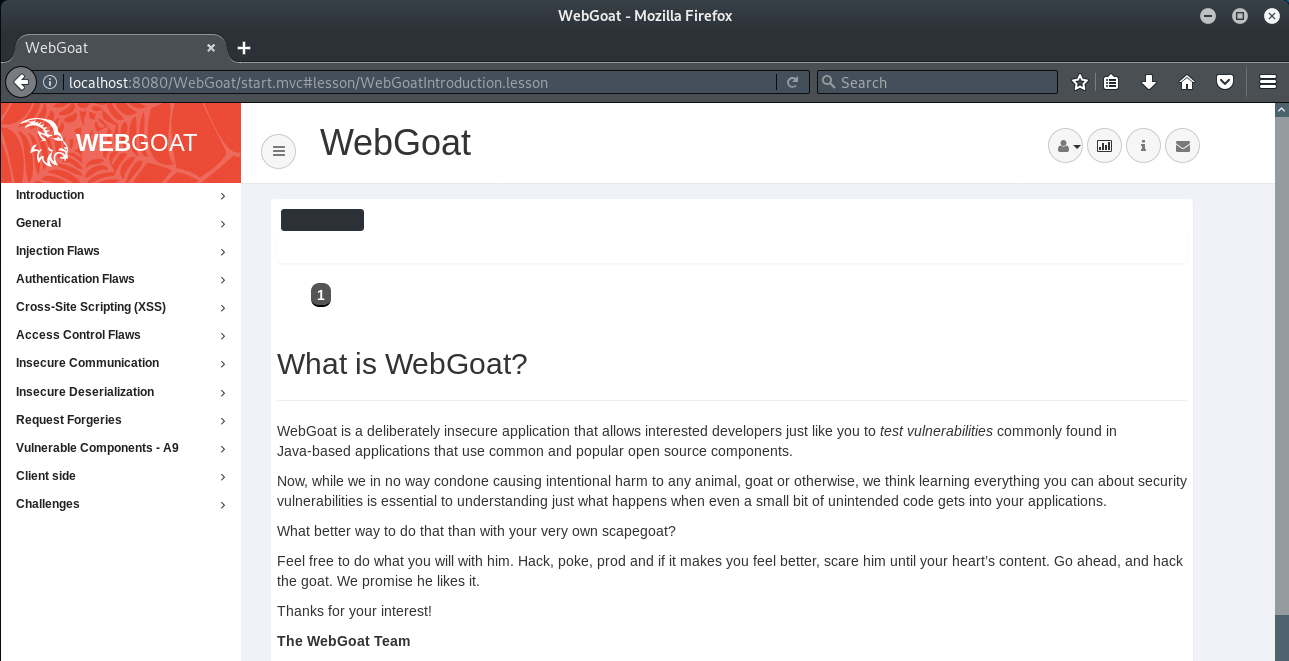
WebGoat is a deliberately insecure web application which is designed to teach web application security and is maintained by OWASP. The latest release (version 8) has been significantly improved to explain vulnerabilities such as SQL Injection and Cross-Site Scripting (XSS) and contains lessons that allow users to demonstrate their understanding by exploiting vulnerabilities in the application. Descriptions of possible mitigation scenarios are also provided.
Installing Java
WebGoat requires installation of the Java Runtime Environment (JRE). If you already have Java installed, it is worth updating to the latest version to avoid any possible issues.
First, update the package index:
sudo apt-get update
Then install the JRE by running this command:
sudo apt-get install default-jre
To check the Java version after installing the package:
java -version
Installing WebGoat
Download and install the latest version of WebGoat Server to a suitable location, such as your Downloads folder.
All releases can be found here: https://github.com/WebGoat/WebGoat/releases
The latest version (at the time of writing) is: webgoat-server-8.0.0.M23.jar
wget https://github.com/WebGoat/WebGoat/releases/download/v8.0.0.M23/webgoat-server-8.0.0.M23.jar
To start the WebGoat Server:
java -jar webgoat-server-8.0.0.M23.jar
Note: if using Java 9 or higher you might need to start WebGoat as follows (update version number as required):
java --add-modules java.xml.bind -jar webgoat-server-8.0.0.M23.jar
You will see the following message when WebGoat has started successfully:
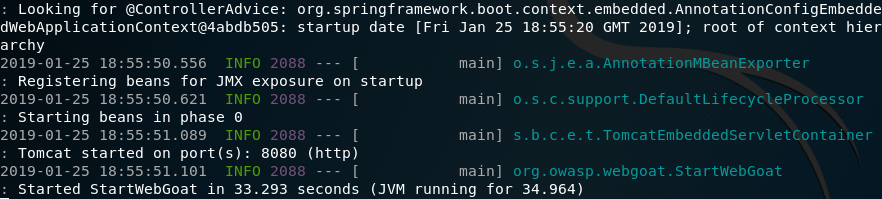
Note: if you wish to run WebGoat on an alternate port and address, you can do so with the following options:
java -jar webgoat-server-8.0.0.M23.jar [--server.port=8080] [--server.address=localhost]
Accessing the WebGoat Interface
To access the WebGoat interface, open your browser and navigate to:
http://localhost:8000/WebGoat
You will then be presented with the WebGoat login screen:
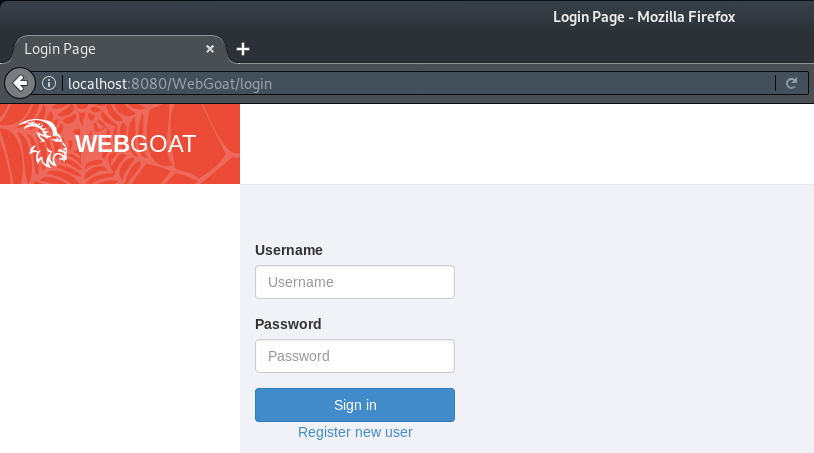
To access the lessons and challenges you will need to select 'Register new user' and create a login.
Note the terms of use when creating a new user:
While running this program your machine will be extremely vulnerable to attack. You should disconnect from the Internet while using this program. WebGoat's default configuration binds to localhost to minimize the exposure.
This program is for educational purposes only. If you attempt these techniques without authorization, you are very likely to get caught. If you are caught engaging in unauthorized hacking, most companies will fire you. Claiming that you were doing security research will not work as that is the first thing that all hackers claim.
Once you are logged in, then it's time to get started:
Please feel free to contact me via Twitter and thanks for reading.